Securing Gradle Builds
Every Gradle build pulls in code from external repositories, executes tools you didn’t author, and publishes artifacts that others will trust. Each step is a potential attack surface.
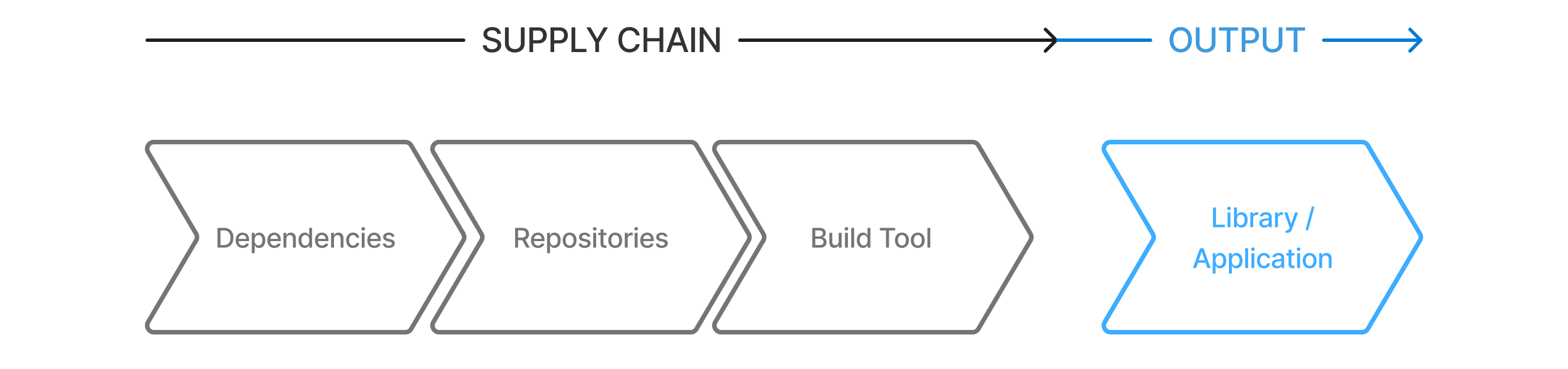
For a typical Gradle build, the supply chain has three main components:
-
Dependencies – Libraries and plugins your project consumes.
-
Repositories – Where artifacts are stored and served.
-
Build Tool – Gradle itself.
Attacks can originate at any layer and then propagate downstream through published artifacts, transitive dependencies, or compromised tools.
Even the build tool itself is an attack vector.
Common issues and attacks include:
-
Dependencies
-
Typosquatting
-
Compromised artifacts
-
Silent version drift
-
-
Repositories
-
Using unauthorized public repositories
-
Leaking secure package names
-
Artifacts from unauthenticated repositories
-
-
Build Tool
-
Poisoned caches
-
Compromised CI
-
Compromised wrapper
-
Gradle provides features to harden each part of this chain:
-
Dependencies – Validate libraries and plugins using checksums and signatures.
-
Repositories – Centralize repository definitions and use trusted mirrors.
-
Build Tool – Verify the Gradle distribution and Wrapper JAR file using checksums.